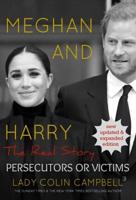
Publisher's Synopsis
Introduction
This course is designed to provide a comprehensive introduction to the world of cyber security tools. Participants will learn how these tools can help protect their data, networks, and systems from malicious attacks. This course will cover topics such as identification and prevention of common threats, understanding how different software applications can be used for protection, and tips for configuring network settings for optimum security.
Additionally, participants will have the opportunity to gain hands-on experience with a range of popular open source and commercial cyber security tools.
1. Demonstrate an understanding of basic cyber security concepts and terminology.
2. Explain the roles and responsibilities of a cyber security specialist.
3. Recognize types of cyber-attacks, malicious software, defense against them, and prevention through policy enforcement.
4. Identify best practices associated with various cybersecurity tools such as firewalls, intrusion detection systems (IDS), virtual private networks (VPNs), network monitoring tools, and identity & access management systems (IAM).
5. Understand risk assessment techniques for developing comprehensive cybersecurity strategies in response to vulnerabilities in a system or business operations.
6. Discuss the importance of threat intelligence and incident management in addressing cyber threats quickly and efficiently.
7. Illustrate how encryption technologies are used to increase data protection from unauthorized access by third parties or malicious attackers.
8. Describe technical solutions for responding to post-incident investigations including forensics analysis, data recovery options, security patching methods, system remediation plans, and long-term risk mitigation strategies based on regulations like NIST 800-53 or ISO 27001/2 standards. Course Outline
Module 1. Introduction to Cybersecurity Tools
a. Overview of cybersecurity threats and protections
b. Understanding the importance of risk management.
c. Key concepts in network security
Module 2. Network Security Scanning Tools
a. Identifying vulnerabilities using NMAP, Wireshark etc.
b. Configuring perimeter firewalls and IDS/IPS systems.
c. Troubleshooting poor security systems' performance.
Module 3. Authentication Policies & Procedures
a. Access control principles and authentication models
b. Authentication protocols and implementation techniques
Module 4. Data Protection Mechanisms & Encryption Tools
a. Exploring data protection tools such as PGP, SSL, etc.
b. Establishing secure communication practices for remote access users.
c. Implementing encryption techniques for data storage and transmission.
d. Ensuring an appropriate level of security is provided onsite servers and networks.
Module 5. Risk Analysis & Incident Response Planning
a. Analyzing potential attack vectors and assessing areas of vulnerability.
b. Developing incident response plans to address malware threats.
c. Maintaining up-to-date information regarding industry trends in cybercrime.
d. Working with stakeholders to develop appropriate standards for automated processes.
Module 6. Disaster Recovery & Business Continuity Strategies
a. Creating disaster recovery plans to ensure business continuity during times of emergency.
b. Testing existing backup operations capabilities
c. Investigating new technologies for faster response times.
Module 7. Advanced Cybersecurity Tools & Techniques
a. Learning about leading-edge techniques for identifying malicious activities.
b. Exploring forensic analysis tools such as EnCase, FTK etc.
.